
Microsoft Purview Data Loss Prevention
In Microsoft 365, you implement data loss prevention by defining and applying DLP policies.
What is Microsoft Purview Data Loss Prevention?
In Microsoft 365, you implement data loss prevention by defining and applying DLP policies. Organizations have sensitive information under their control such as financial data, proprietary data, credit card numbers, health records, or social security numbers. To help protect this sensitive data and reduce risk, they need a way to prevent their users from inappropriately sharing it with people who shouldn't have it. This practice is called data loss prevention (DLP).
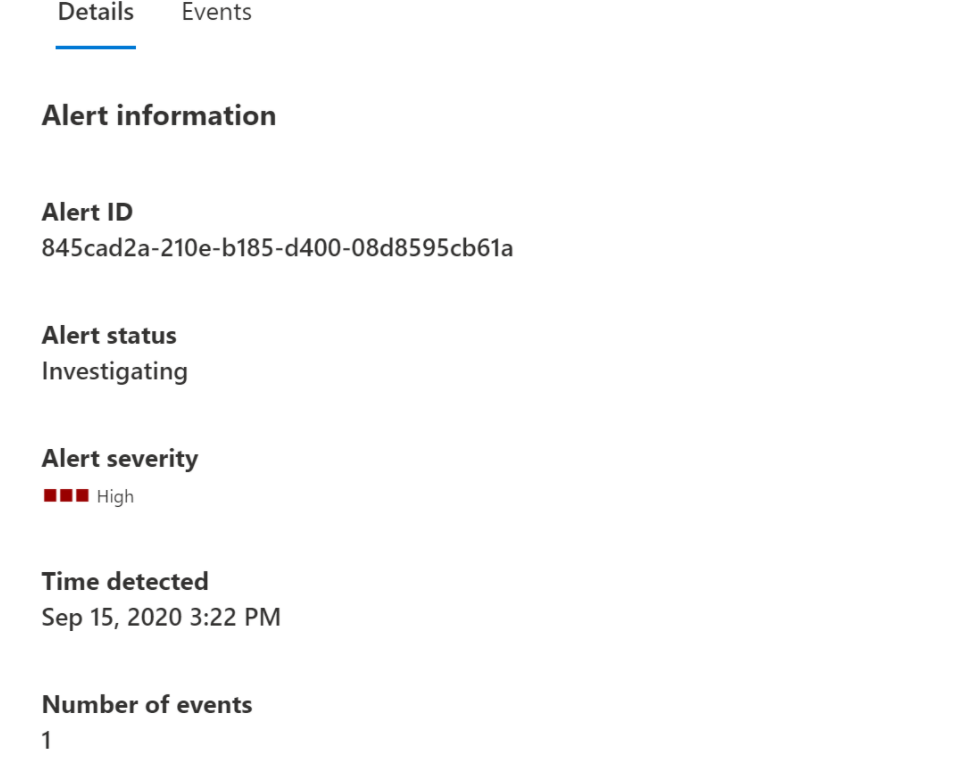
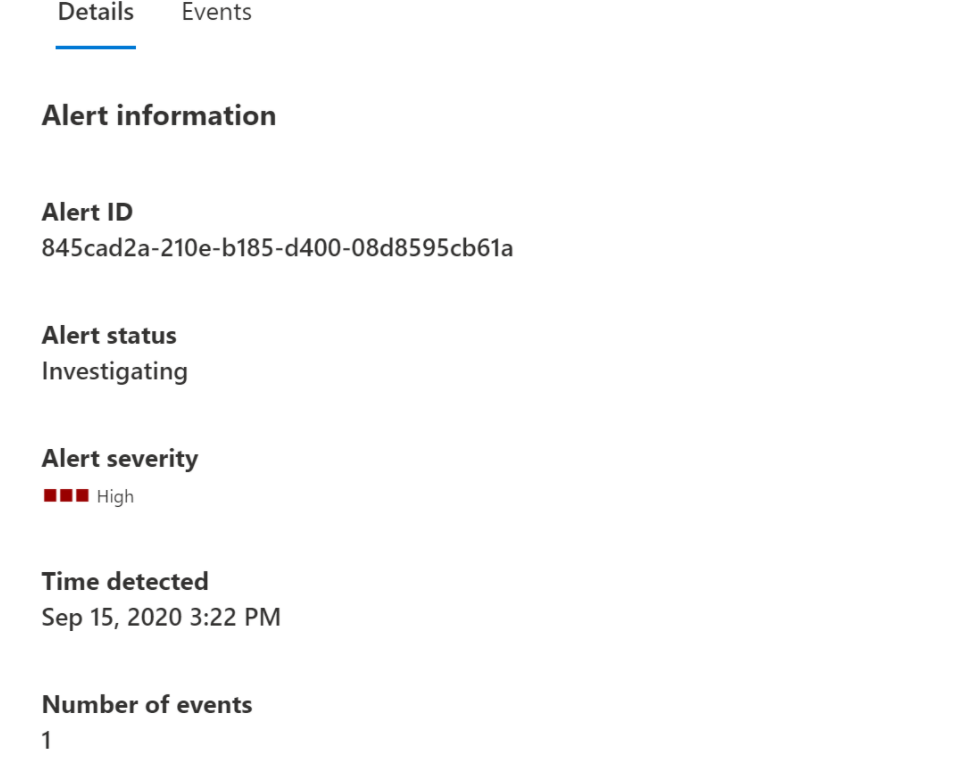
Screenshots
Video
Categories
FAQ
The official website of Microsoft Purview Data Loss Prevention is http://www.microsoft.com/
In Microsoft 365, you implement data loss prevention by defining and applying DLP policies. Organizations have sensitive information under their control such as financial data, proprietary data, credit card numbers, health records, or social security numbers. To help protect this sensitive data and reduce risk, they need a way to prevent their users from inappropriately sharing it with people who shouldn't have it. This practice is called data loss prevention (DLP).
Microsoft Purview Data Loss Prevention belongs to the Data Loss Prevention category.
No, Microsoft Purview Data Loss Prevention does not offer a free trial.
Reviews(0)
Write a reviewMicrosoft Purview Data Loss Prevention alternatives

TeamViewer
TeamViewer is widely used by small businesses for remote support and desktop access, especially in IT and software services. It stands out for its secure access controls and screen sharing, though pricing and support policies are common concerns. Rec...load more

Malwarebytes for Business
Malwarebytes for Business is a cybersecurity platform that protects laptops, servers, and mobile devices against threats. The endpoint security portfolio combines layers of protection and threat intelligence to secure organizations from threats, incl...load more

Google Cloud
Google Cloud Platform is cloud-based suite of solutions that allows users to create anything from websites to complex applications for businesses of all sizes across a range of industries. Google Cloud Platform offers a scalable data warehouse powere...load more

ESET Endpoint Security
ESET Endpoint Security, a leading solution in the computer security category, is designed for businesses with 250+ employees, offering both cloud-based and on-premises options for comprehensive internet security and malware protection. Renowned globa...load more

NAKIVO Backup & Replication
NAKIVO Backup & Replication is a comprehensive data protection solution for physical Windows and Linux servers as well as virtual and SaaS environments. The solution is designed to create incremental backups of physical servers with support for appli...load more

NinjaOne
NinjaOne empowers small IT teams to manage endpoints, automate patching, and monitor devices across Windows, Mac, and Linux systems. Its most used by IT service providers and software services firms. Reviewers highlight its fast setup and automation ...load more

Webroot Business Endpoint Protection
Multi-vector protection against viruses and malware offering full protection against all of today's sophisticated malware threats including Trojans, keyloggers, phishing, spyware, back-doors, rootkits, zero-day and advanced persistent threats. Built ...load more

Cove Data Protection
Cove Data Protection, from N-able, is a cloud-first backup and disaster recovery service for servers, workstations, and Microsoft 365, all managed from a multitenant web-based dashboard. Cove was created and optimized for the cloud, so incremental ba...load more

Iperius Backup
Iperius Backup for Servers, VMware ESXi, Hyper-V, SQL Server, MySQL, Microsoft 365 - To Cloud, NAS, RDX, Tape, FTP, Google Drive, S3.

Carbonite
Industry-leading data protection system which helps businesses of all sizes through data encryption, compliance, file management and cloud backup. Protect against accidental deletion, theft, hardware failure, and data corruption. Restore data followi...load more